mirror of
https://github.com/go-gitea/gitea.git
synced 2025-10-25 22:41:25 +02:00
Resolve #31609 This PR was initiated following my personal research to find the lightest possible Single Sign-On solution for self-hosted setups. The existing solutions often seemed too enterprise-oriented, involving many moving parts and services, demanding significant resources while promising planetary-scale capabilities. Others were adequate in supporting basic OAuth2 flows but lacked proper user management features, such as a change password UI. Gitea hits the sweet spot for me, provided it supports more granular access permissions for resources under users who accept the OAuth2 application. This PR aims to introduce granularity in handling user resources as nonintrusively and simply as possible. It allows third parties to inform users about their intent to not ask for the full access and instead request a specific, reduced scope. If the provided scopes are **only** the typical ones for OIDC/OAuth2—`openid`, `profile`, `email`, and `groups`—everything remains unchanged (currently full access to user's resources). Additionally, this PR supports processing scopes already introduced with [personal tokens](https://docs.gitea.com/development/oauth2-provider#scopes) (e.g. `read:user`, `write:issue`, `read:group`, `write:repository`...) Personal tokens define scopes around specific resources: user info, repositories, issues, packages, organizations, notifications, miscellaneous, admin, and activitypub, with access delineated by read and/or write permissions. The initial case I wanted to address was to have Gitea act as an OAuth2 Identity Provider. To achieve that, with this PR, I would only add `openid public-only` to provide access token to the third party to authenticate the Gitea's user but no further access to the API and users resources. Another example: if a third party wanted to interact solely with Issues, it would need to add `read:user` (for authorization) and `read:issue`/`write:issue` to manage Issues. My approach is based on my understanding of how scopes can be utilized, supported by examples like [Sample Use Cases: Scopes and Claims](https://auth0.com/docs/get-started/apis/scopes/sample-use-cases-scopes-and-claims) on auth0.com. I renamed `CheckOAuthAccessToken` to `GetOAuthAccessTokenScopeAndUserID` so now it returns AccessTokenScope and user's ID. In the case of additional scopes in `userIDFromToken` the default `all` would be reduced to whatever was asked via those scopes. The main difference is the opportunity to reduce the permissions from `all`, as is currently the case, to what is provided by the additional scopes described above. Screenshots:   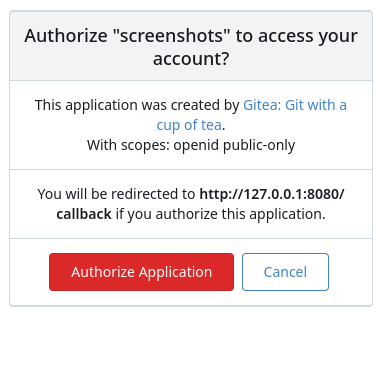  --------- Co-authored-by: wxiaoguang <wxiaoguang@gmail.com>
36 lines
1.0 KiB
Go
36 lines
1.0 KiB
Go
// Copyright 2024 The Gitea Authors. All rights reserved.
|
|
// SPDX-License-Identifier: MIT
|
|
|
|
package oauth2_provider //nolint
|
|
|
|
import (
|
|
"testing"
|
|
|
|
"github.com/stretchr/testify/assert"
|
|
)
|
|
|
|
func TestGrantAdditionalScopes(t *testing.T) {
|
|
tests := []struct {
|
|
grantScopes string
|
|
expectedScopes string
|
|
}{
|
|
{"openid profile email", "all"},
|
|
{"openid profile email groups", "all"},
|
|
{"openid profile email all", "all"},
|
|
{"openid profile email read:user all", "all"},
|
|
{"openid profile email groups read:user", "read:user"},
|
|
{"read:user read:repository", "read:repository,read:user"},
|
|
{"read:user write:issue public-only", "public-only,write:issue,read:user"},
|
|
{"openid profile email read:user", "read:user"},
|
|
{"read:invalid_scope", "all"},
|
|
{"read:invalid_scope,write:scope_invalid,just-plain-wrong", "all"},
|
|
}
|
|
|
|
for _, test := range tests {
|
|
t.Run(test.grantScopes, func(t *testing.T) {
|
|
result := GrantAdditionalScopes(test.grantScopes)
|
|
assert.Equal(t, test.expectedScopes, string(result))
|
|
})
|
|
}
|
|
}
|